Managing Remote Team Cybersecurity Risks: A Comprehensive Guide
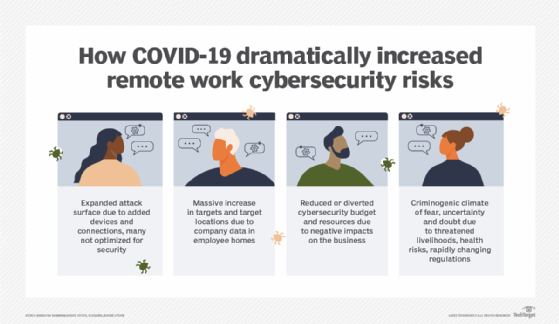
The shift to remote and hybrid work has transformed the way organizations operate, introducing unique cybersecurity challenges that the C-suite must address. As employees access corporate networks from various locations, often using personal devices such as cellphones, the risk of cyber attacks and data breaches increases significantly.
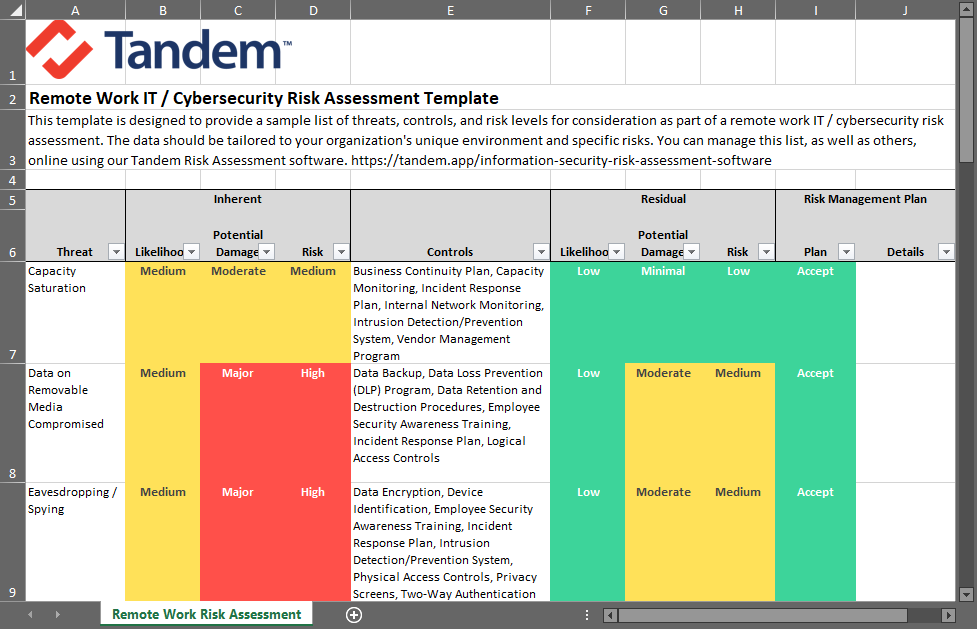
Common Security Risks for Remote and Hybrid Workforces
- Network Vulnerability: Home networks remain significantly less secure than enterprise environments, making them a primary entry point for attackers.
- Identity-Based Attacks: With employees accessing corporate systems from personal devices, identity-based attacks become more prevalent, putting sensitive data at risk.
- Endpoint Vulnerabilities: Remote workers often use laptops, smartphones, and other devices that may not be adequately secured, creating endpoint vulnerabilities that can be exploited by attackers.
- Cloud Access Exposure: Cloud services have become essential for remote work, but they also increase the attack surface, making it crucial to enforce proper access controls and security measures.

Managing Remote Team Cybersecurity Risks: Strategies and Solutions
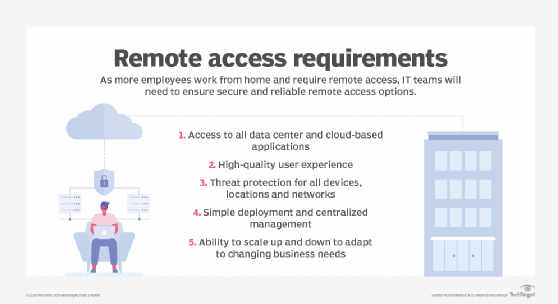
Managing remote team cybersecurity risks requires a proactive approach that involves implementing robust security measures and policies, as well as regular training and awareness programs for employees. Here are some strategies and solutions to consider:
Conclusion

Such details provide a deeper understanding and appreciation for Managing Remote Team Cybersecurity Risks.
Managing remote team cybersecurity risks requires a comprehensive approach that involves implementing robust security measures, policies, and regular training and awareness programs. By understanding the common security risks associated with remote work and implementing the right strategies and solutions, organizations can safeguard their sensitive data and systems from evolving cyber threats.
Best Practices for Managing Remote Team Cybersecurity Risks
- Implement centralized management and access controls to monitor and control access in real-time.
- Implement cyber hygiene practices, such as regular software updates and antivirus scans.
- Implement secure device management policies, including remote wipe and lock.
- Implement cloud security measures, such as encryption and access controls.
- Regularly train and aware employees on cybersecurity best practices and potential security threats.