Protecting Your Cloud Infrastructure: The Imperative of Malware Protection for Cloud Infrastructure Security
In today's digital landscape, businesses are increasingly relying on cloud infrastructure to host their applications, data, and workloads. However, this shift to the cloud has also introduced new security risks, including malware threats that can compromise the integrity and security of cloud-based resources.
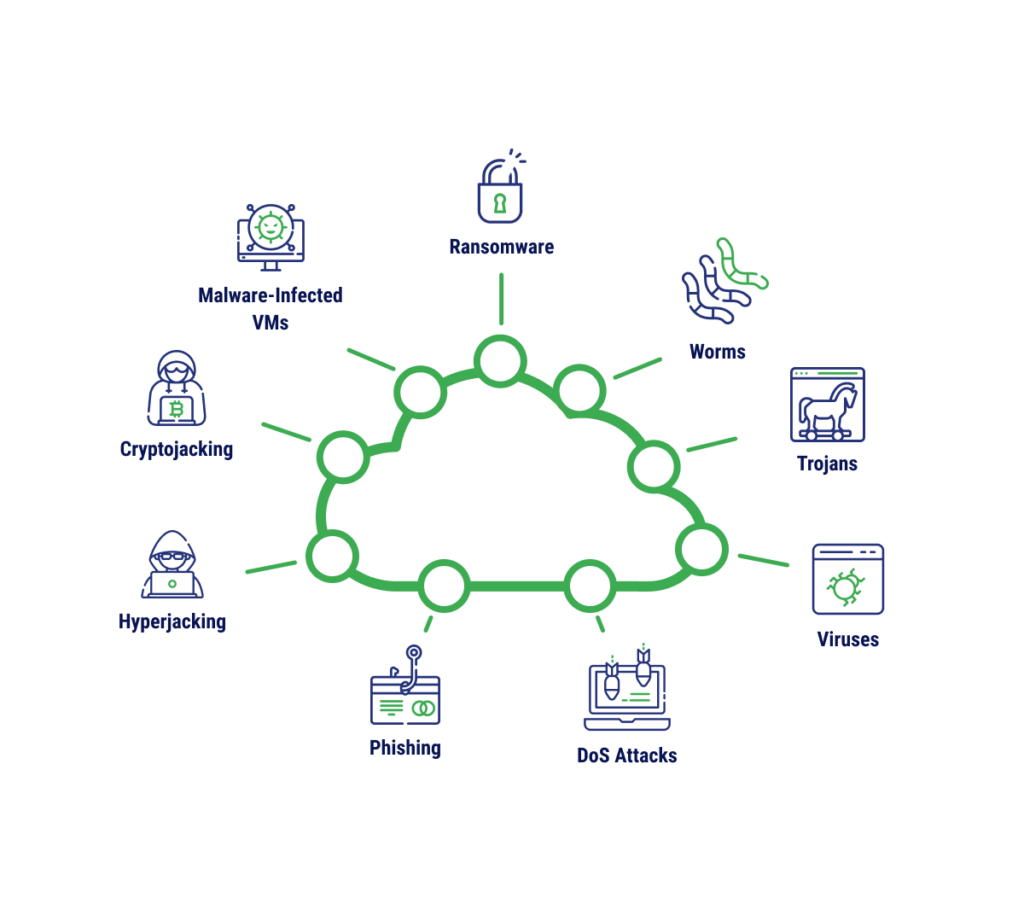
The Growing Threat of Malware in the Cloud
Malware, or malicious software, is a type of cyber threat that can infiltrate and damage cloud-based systems, applications, and data. In the cloud, malware can spread quickly and cause significant harm, leading to data breaches, downtime, and financial losses. According to various reports, the prevalence of malware attacks has grown significantly in recent years, underscoring the need for robust malware protection for cloud infrastructure security.
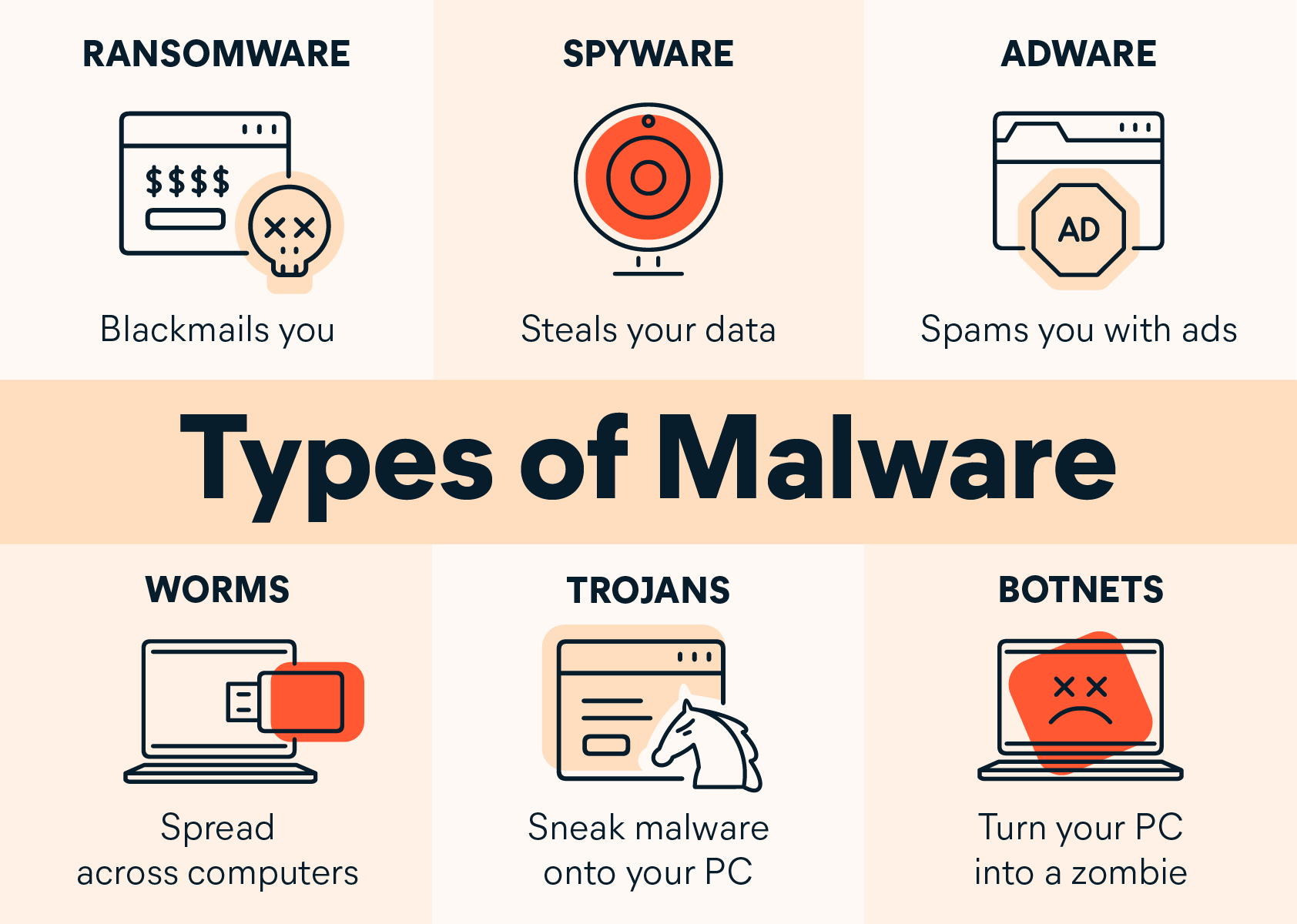
- Cloud malware types: Malware threats in the cloud can be categorized into several types, including Adware, ransomware, Trojans, Spyware, and Scareware, among others.
- Malware risks and consequences: Malware attacks can compromise cloud-based resources, leading to data breaches, downtime, and financial losses.
- Implementation of malware protection: Organizations can implement various measures to prevent and detect malware attacks, including using antimalware tools, implementing intrusion detection systems, and training users on cybersecurity best practices.
Cloud Infrastructure Security and Malware Protection
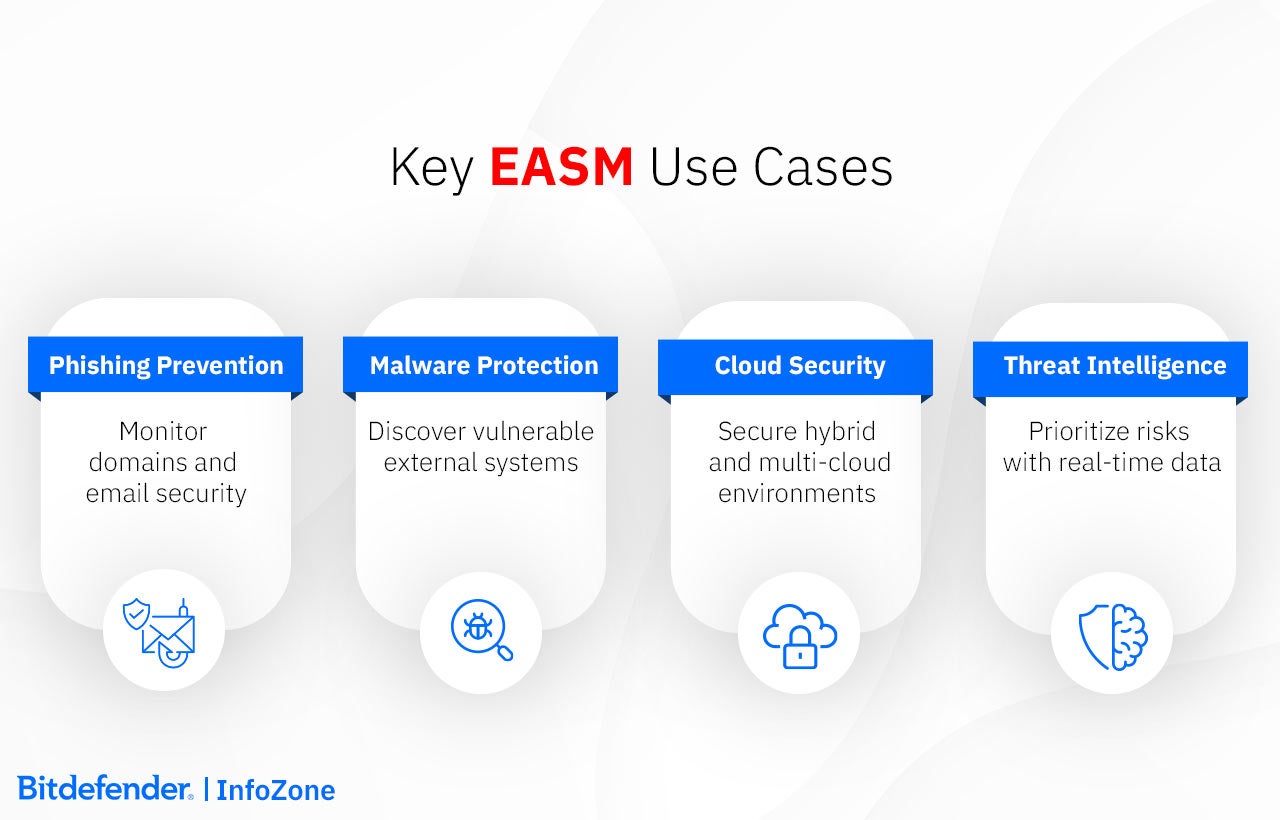
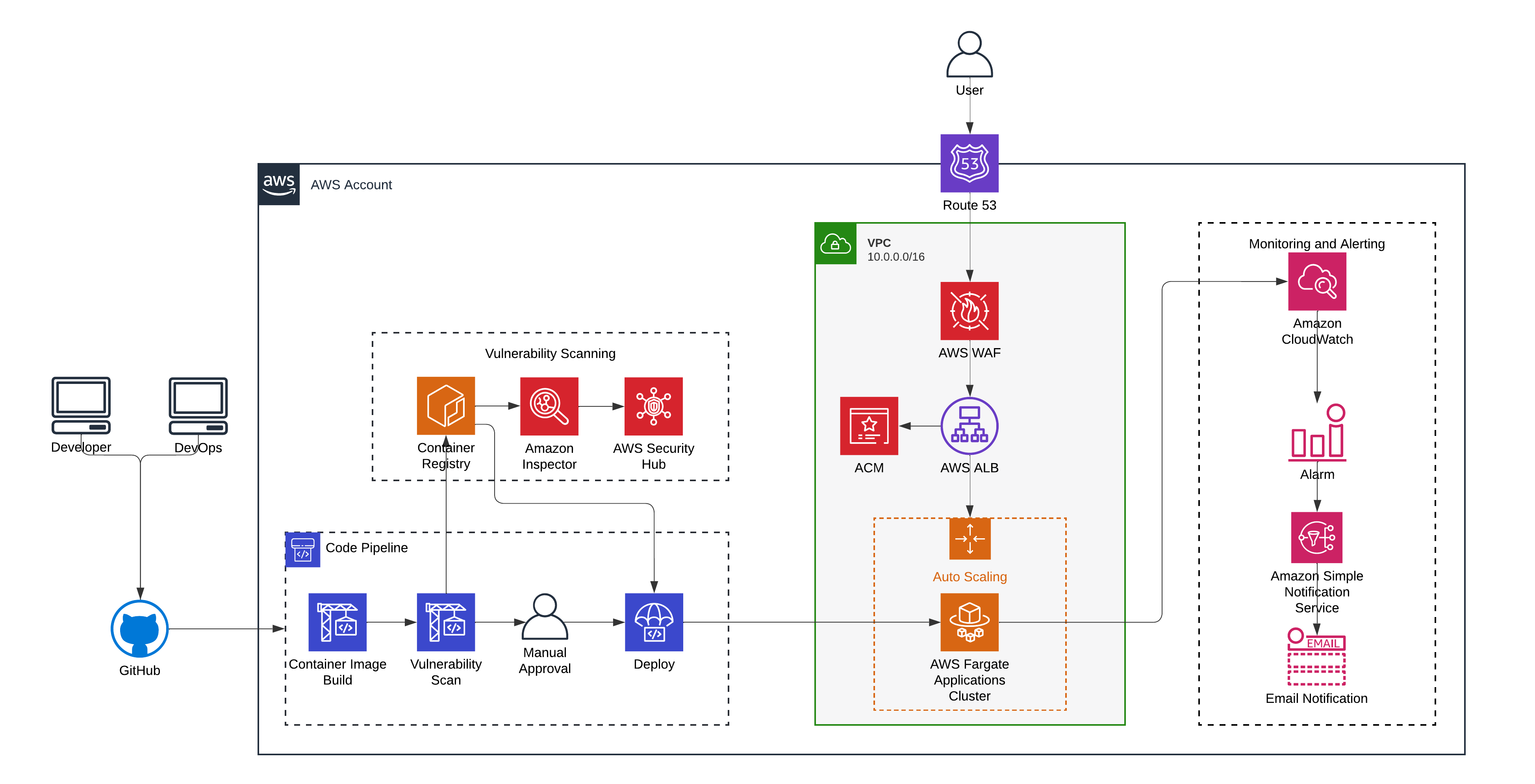
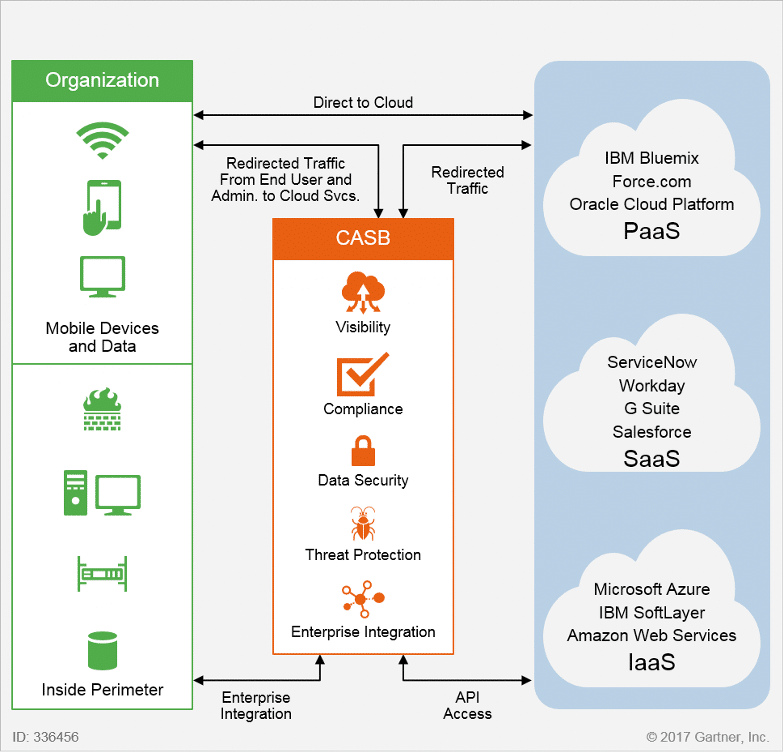
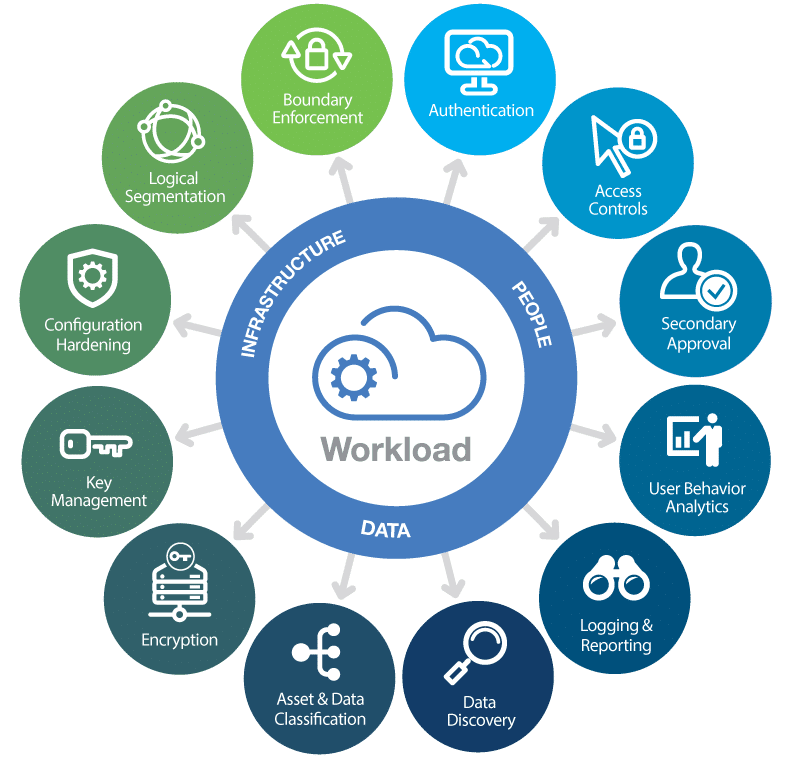
Cloud infrastructure security refers to the processes, technologies, and practices used to protect cloud-based resources from cyber threats, including malware attacks. In order to ensure the security of cloud-based resources, organizations must implement robust malware protection measures, including:
- Cloud security posture management (CSPM): CSPM involves monitoring and managing the security posture of cloud-based resources to identify vulnerabilities and misconfigurations.
- Cloud workload protection platform (CWPP): CWPP involves protecting cloud-based workloads from malware attacks and other cyber threats.
- Anti-malware protection: Anti-malware protection involves using antimalware tools to detect and block malware attacks in real-time.
Best Practices for Malware Protection in the Cloud

To ensure the security of cloud-based resources, organizations should follow best practices for malware protection, including:
- Implementing antimalware tools: Organizations should implement antimalware tools to detect and block malware attacks in real-time.
- Training users on cybersecurity best practices: Users should be trained on cybersecurity best practices, including avoiding suspicious emails and links, and using strong passwords.
- Monitoring and logging: Organizations should monitor and log cloud-based resources to identify potential security threats and vulnerabilities.
In conclusion, malware protection for cloud infrastructure security is a critical aspect of cloud security that requires robust measures to prevent and detect malware attacks. By implementing best practices for malware protection, including CSPM, CWPP, anti-malware tools, user training, and monitoring and logging, organizations can ensure the security of cloud-based resources and prevent malware attacks.
Recommended Reading
For more information on cloud security, malware protection, and cybersecurity best practices, readers can refer to the following resources: