G Network Settings for Cybersecurity: A Comprehensive Guide
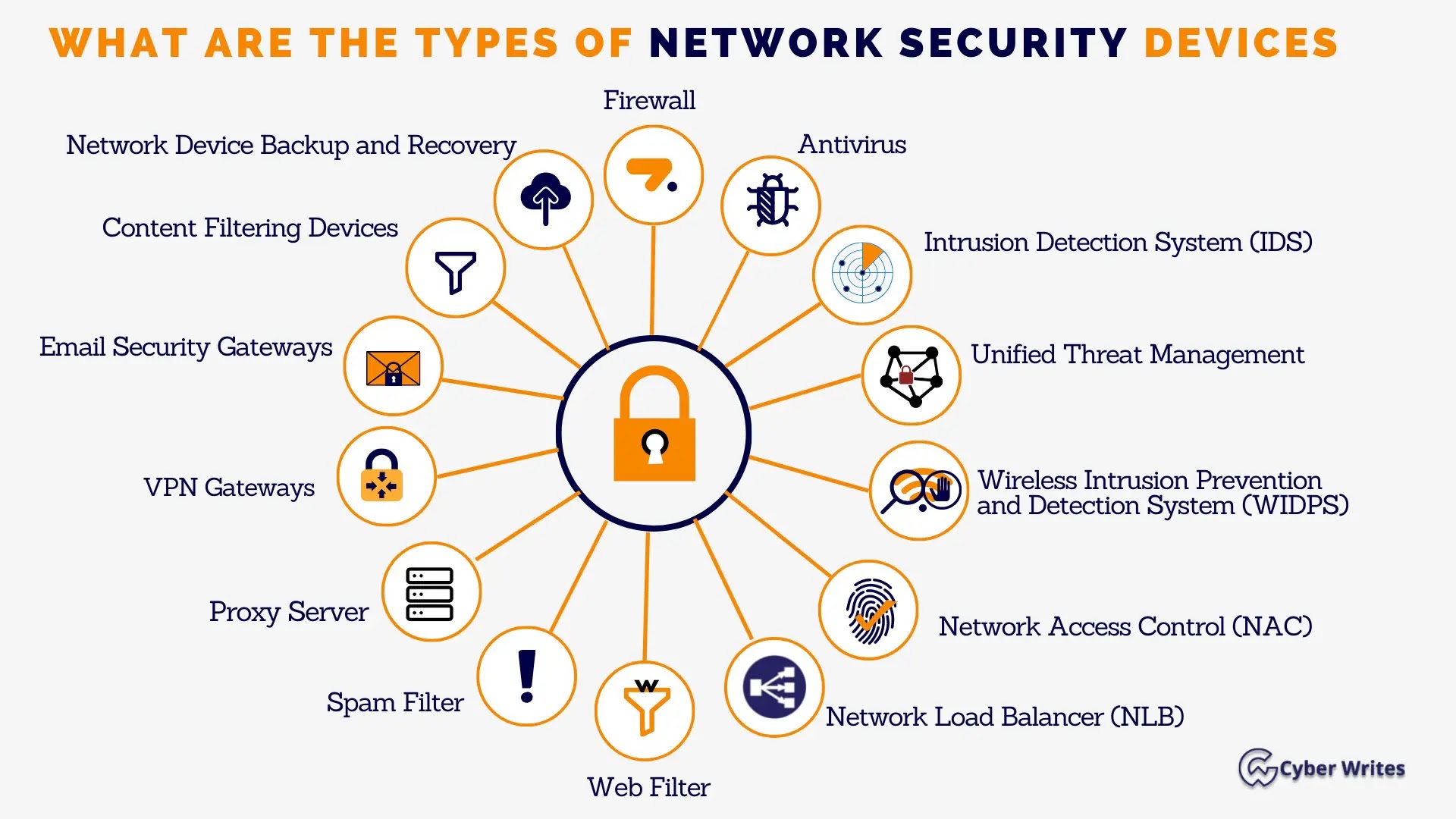
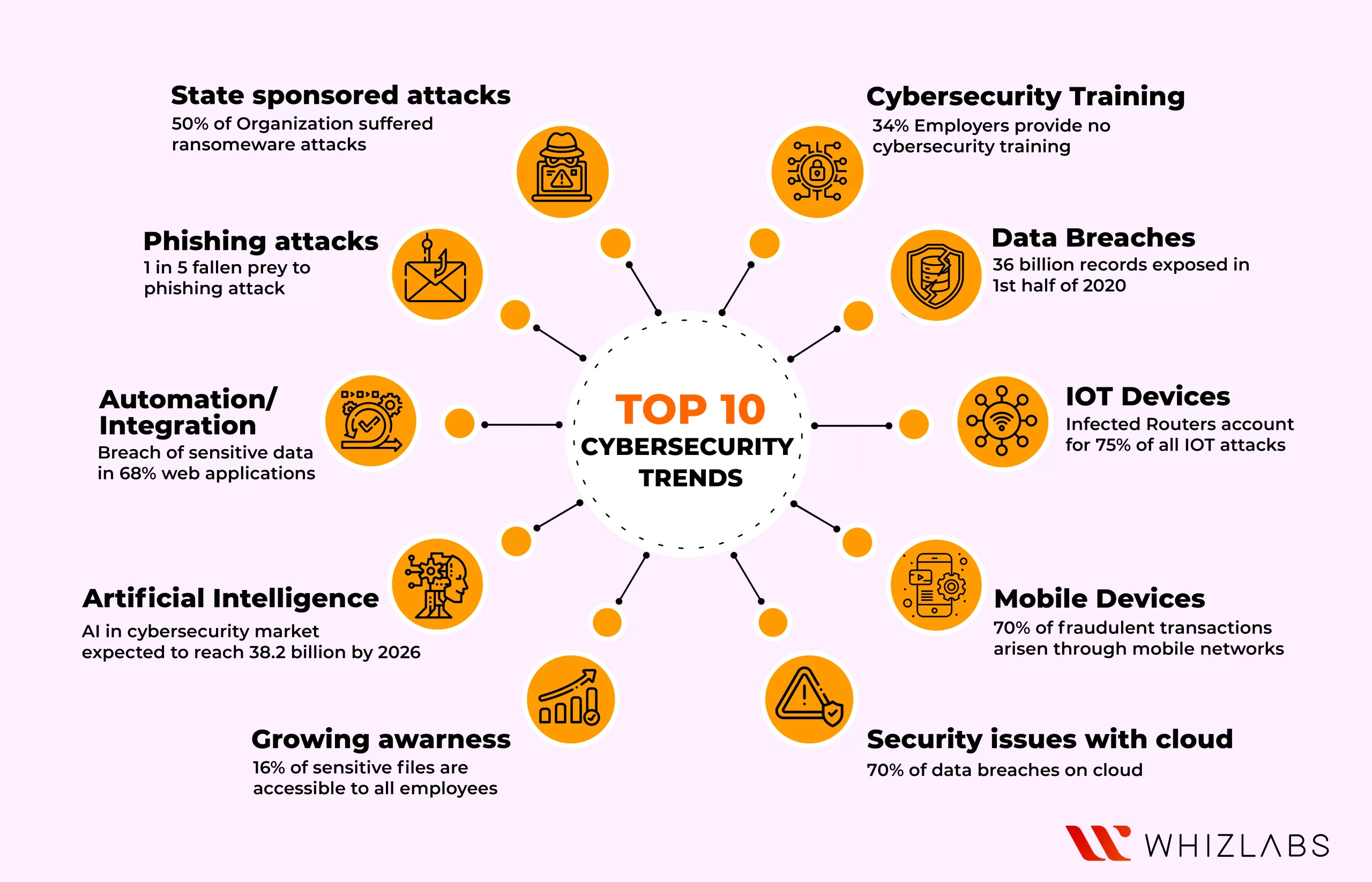
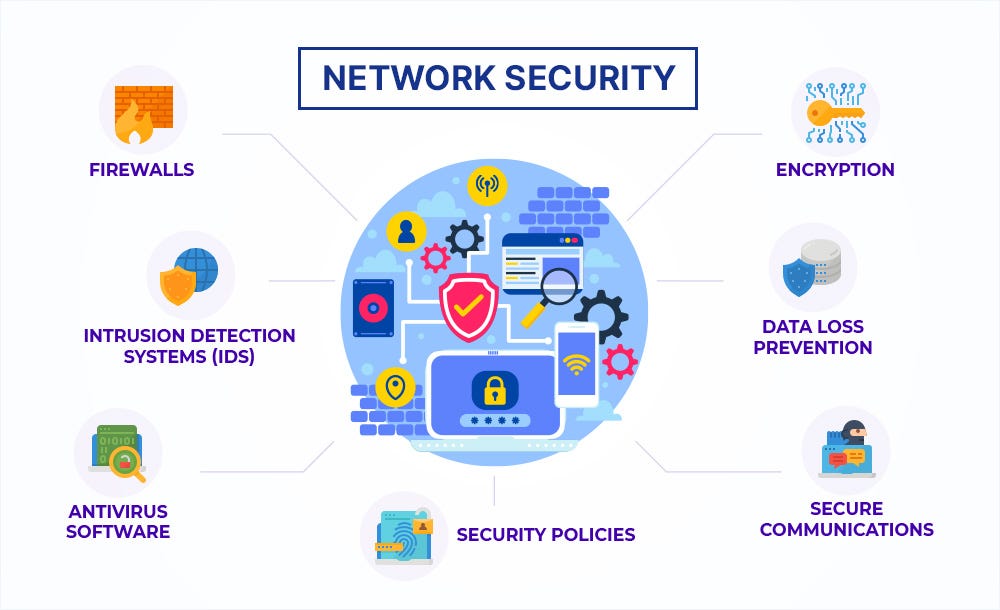
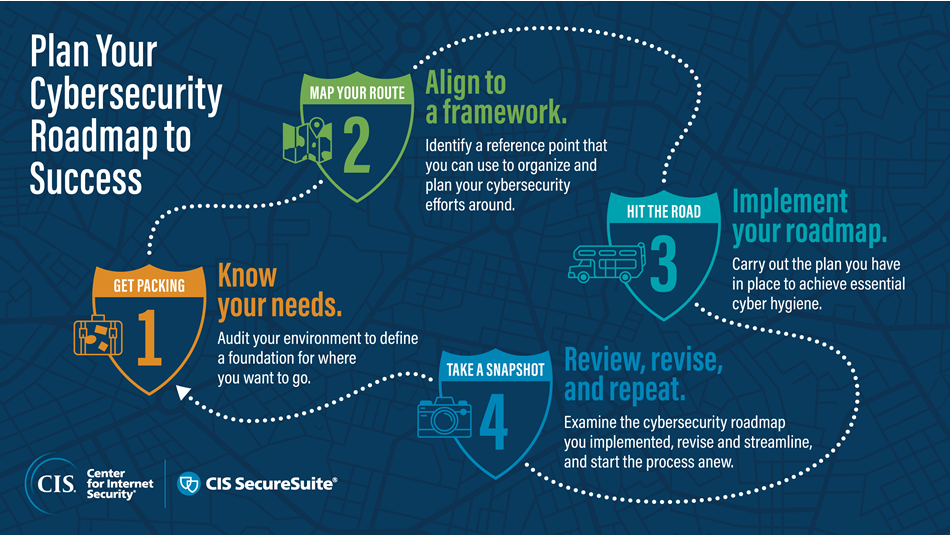
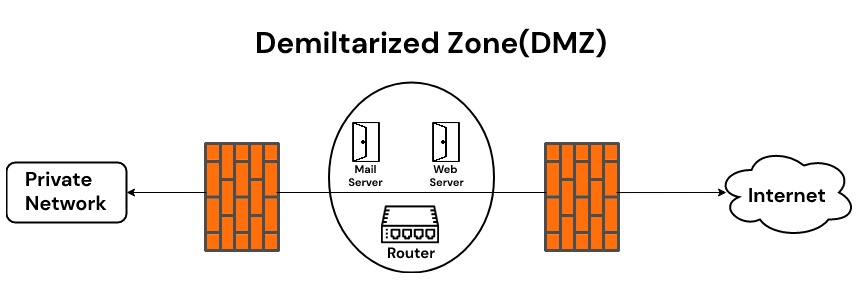
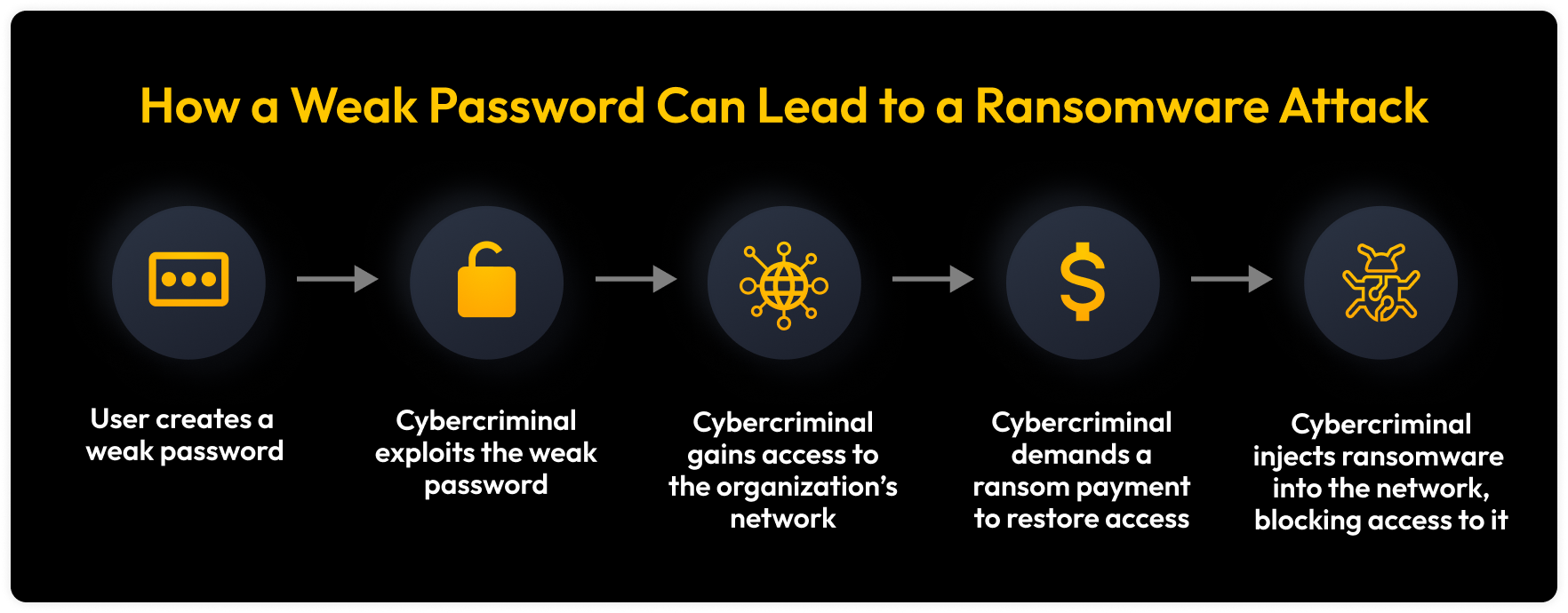
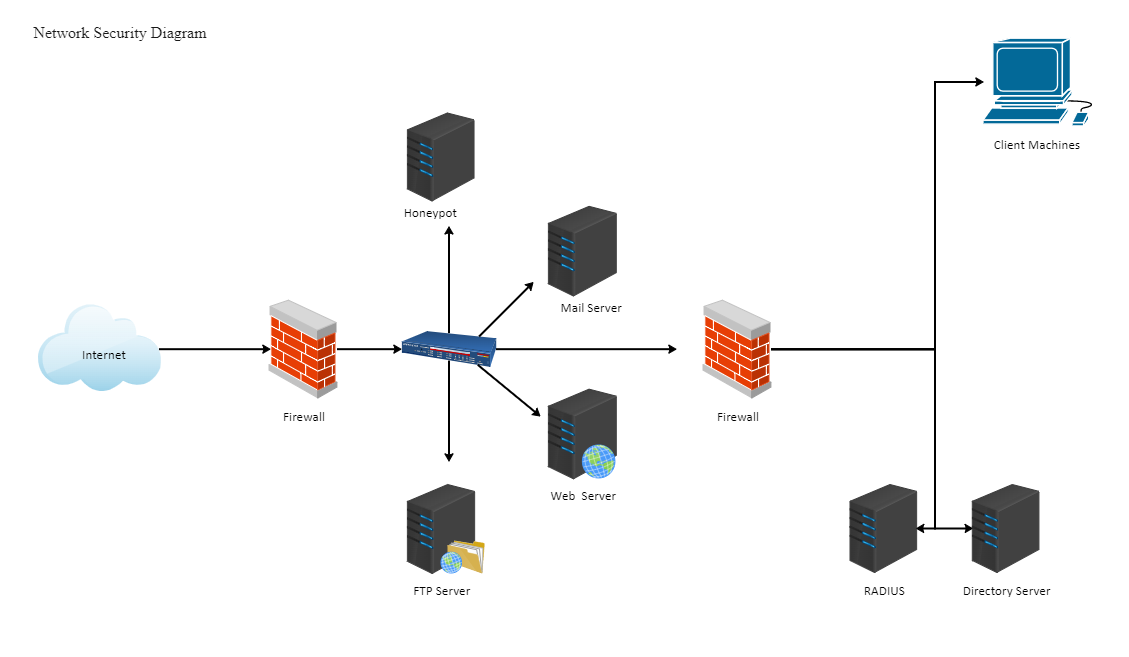
October is Cybersecurity Awareness Month, a time to raise awareness of the importance of cybersecurity in protecting our networks. In this guide, we'll explore the essential G Network settings for cybersecurity and provide you with a detailed checklist to ensure your network is secure. Network security is critical in today's digital age. With the increasing number of cyber threats, it's essential to have a robust security framework in place to protect your network from unauthorized access, data breaches, and malware attacks. A secure network not only protects your sensitive data but also ensures business continuity and reputation.Network Security Checklist
Google Network Settings for Cybersecurity

This particular example perfectly highlights why G Network Settings For Cybersecurity is so captivating.
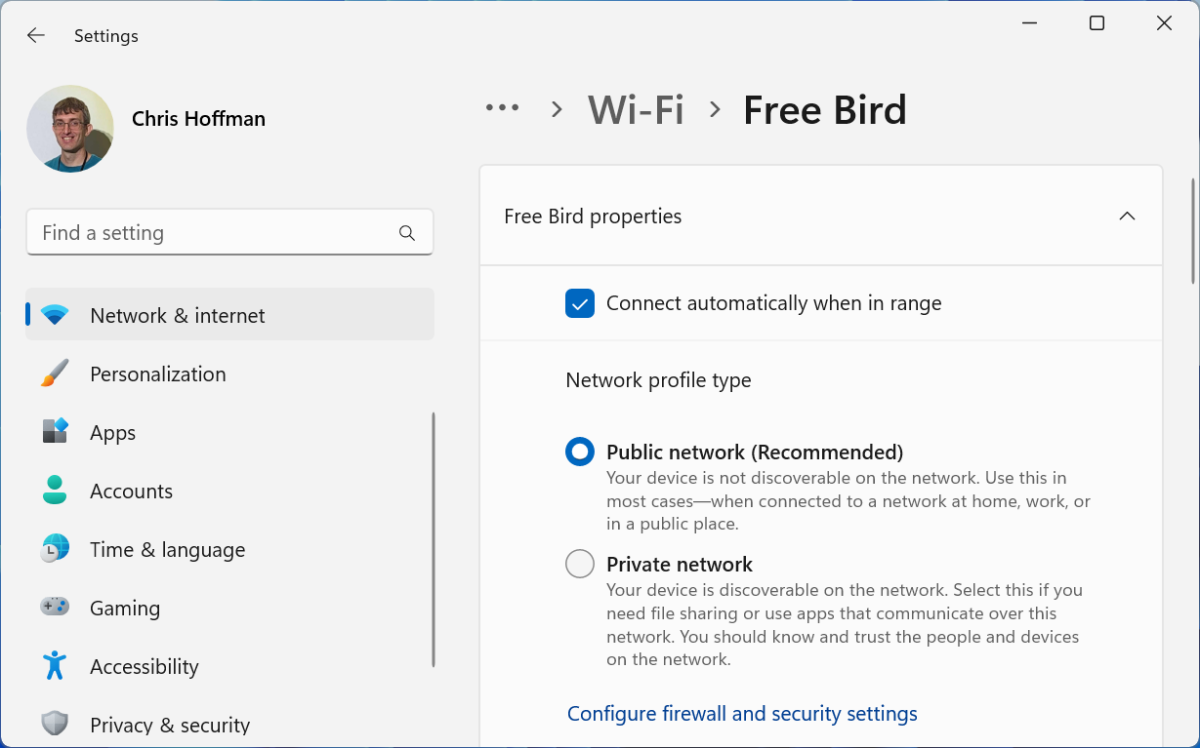
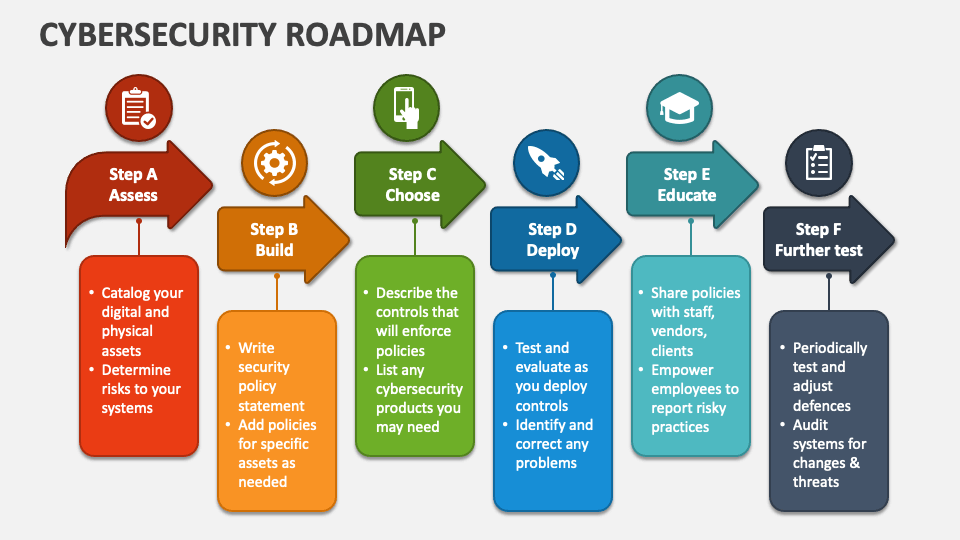
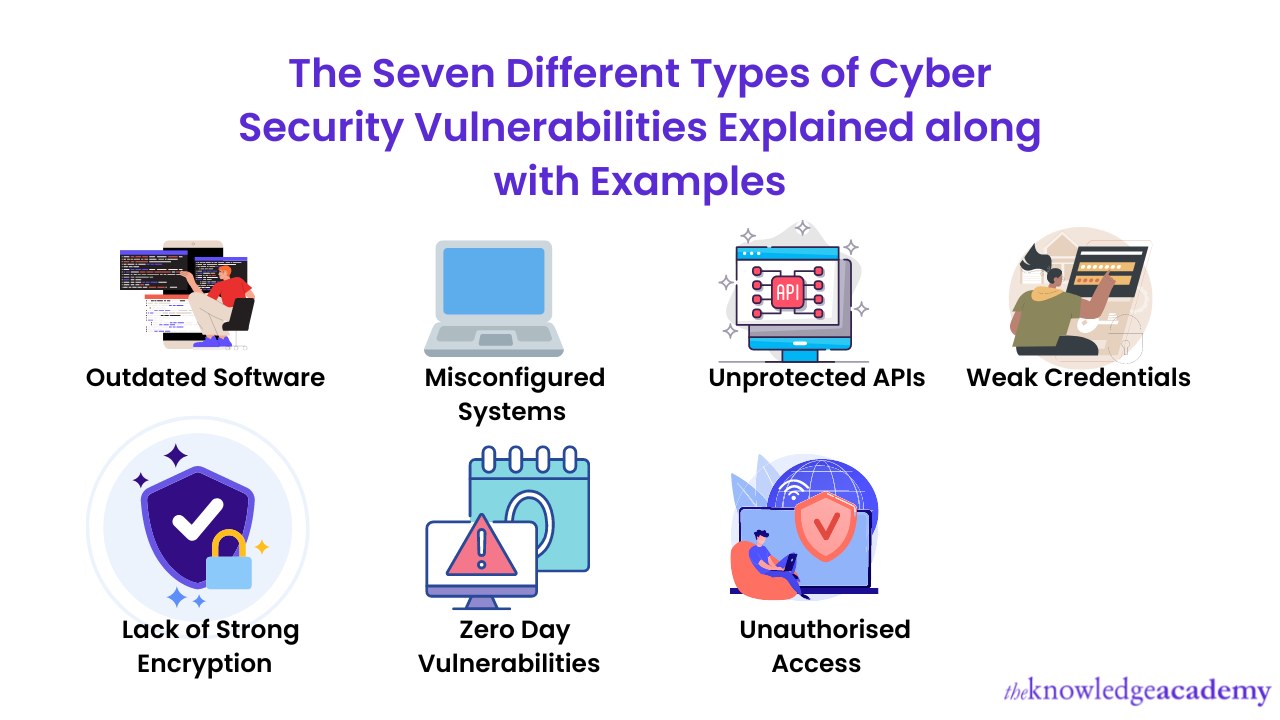
To enhance network security using Google services, follow these settings: ### 1. **Enable Two-Factor Authentication (2FA)** Enable 2FA on all Google accounts to add an extra layer of security. ### 2. **Set Up Advanced Threat Protection** Set up advanced threat protection on Google Workspace to detect and block malware and phishing attacks. ### 3. **Use Secure Protocols** Use secure protocols such as HTTPS and SFTP to encrypt data in transit. ### 4. **Enable Data Loss Prevention (DLP)** Enable DLP on Google Workspace to detect and prevent sensitive data from being exposed. ### 5. **Configure Backup and Archives** Configure backup and archives on Google Workspace to ensure data is safely stored. To maintain a secure network, follow these best practices: ### 1. **Regularly Update Firmware and Software** Regularly update firmware and software to patch security vulnerabilities. ### 2. **Use Strong, Unique Passwords** Use strong, unique passwords for all devices and accounts. ### 3. **Use a Secure Network Configuration Tool** Use a secure network configuration tool to automate and enforce security settings. ### 4. **Monitor Network Activity** Monitor network activity regularly to detect and respond to security incidents. ### 5. **Conduct Regular Security Audits** Conduct regular security audits to identify and address security vulnerabilities.