Ransomware Protection Best Practices: Safeguarding Your Business from Cyber Threats
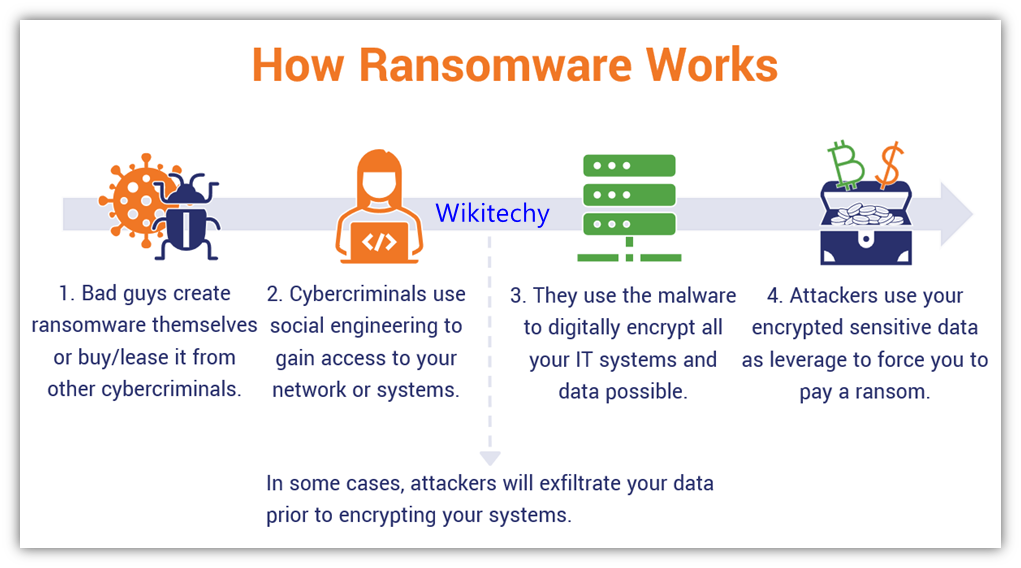
Understanding Ransomware Attacks
Ransomware attacks have become a growing concern for businesses and organizations worldwide. In 2025, the healthcare sector alone faced a 36% surge in ransomware attacks, with over 10.1 million patient records compromised in Q4 of that year. This ever-evolving threat demands immediate attention and action to protect one's organization. This article provides a comprehensive guide on ransomware protection best practices to help you safeguard your business from these cyber threats.Basic Security Measures: The Foundation of Ransomware Protection

- Regular software updates: Ensure that all software, including operating systems and applications, are up-to-date with the latest security patches.
- Strong authentication**: Implement strong authentication measures, such as multi-factor authentication (MFA), to prevent unauthorized access to your systems.
- Malware protection**: Use reputable antivirus software and maintain regular malware scans to detect and remove potential threats.
- Network security measures**: Implement firewalls, intrusion detection and prevention systems, and secure your network connections to prevent unauthorized access.
Implementing Advanced Ransomware Protection Measures

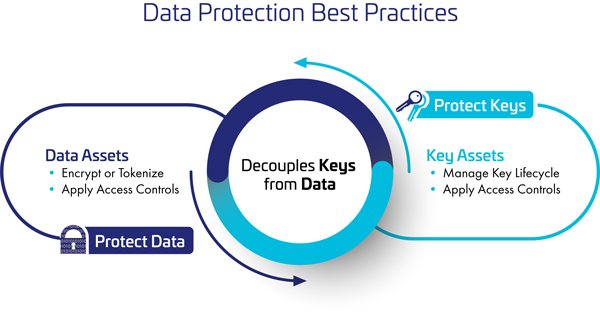
- Encryption**: Implement full-disk encryption, particularly for sensitive data, to prevent attackers from accessing sensitive information.
- Backup and recovery**: Regularly back up your data and maintain a robust backup system to quickly restore data in case of an attack.
- Incident response**: Develop an incident response plan to quickly respond to and contain ransomware attacks.
- Employee education and training**: Educate employees on cybersecurity best practices, including email security and the risks associated with ransomware.
- Monitor for suspicious activity**: Regularly monitor your systems and network for suspicious activity, and implement a continuous monitoring framework to detect and respond to potential threats.
- Keep backups air-gapped**: Store backups offline or on a separate network to prevent ransomware from encroaching on the backup data.
- Use secure protocols**: Implement secure communication protocols, such as Secure Sockets Layer (SSL) or Transport Layer Security (TLS), to protect sensitive information.
- Regularly update and patch systems**: Regularly update and patch all systems, including software and firmware, to ensure you have the latest security vulnerabilities addressed.

Moving forward, it's essential to keep these visual contexts in mind when discussing Ransomware Protection Best Practices.