Protecting Online User Behavior: Essential Guide for a Safe Digital Experience
The internet has become an integral part of our daily lives, making it easier to access information, connect with others, and perform various tasks. However, this widespread use of the internet has also led to numerous security risks and online threats that can compromise our personal data and devices. As a result, protecting online user behavior has become a top priority for individuals and organizations alike.Understanding the Risks and Threats

- Phishing and Scamming: These are the most common online threats, where cybercriminals trick users into revealing sensitive information, such as passwords or credit card numbers.
- Malware and Ransomware: These malicious software can infect devices, leading to data theft, system crashes, or even identity theft.
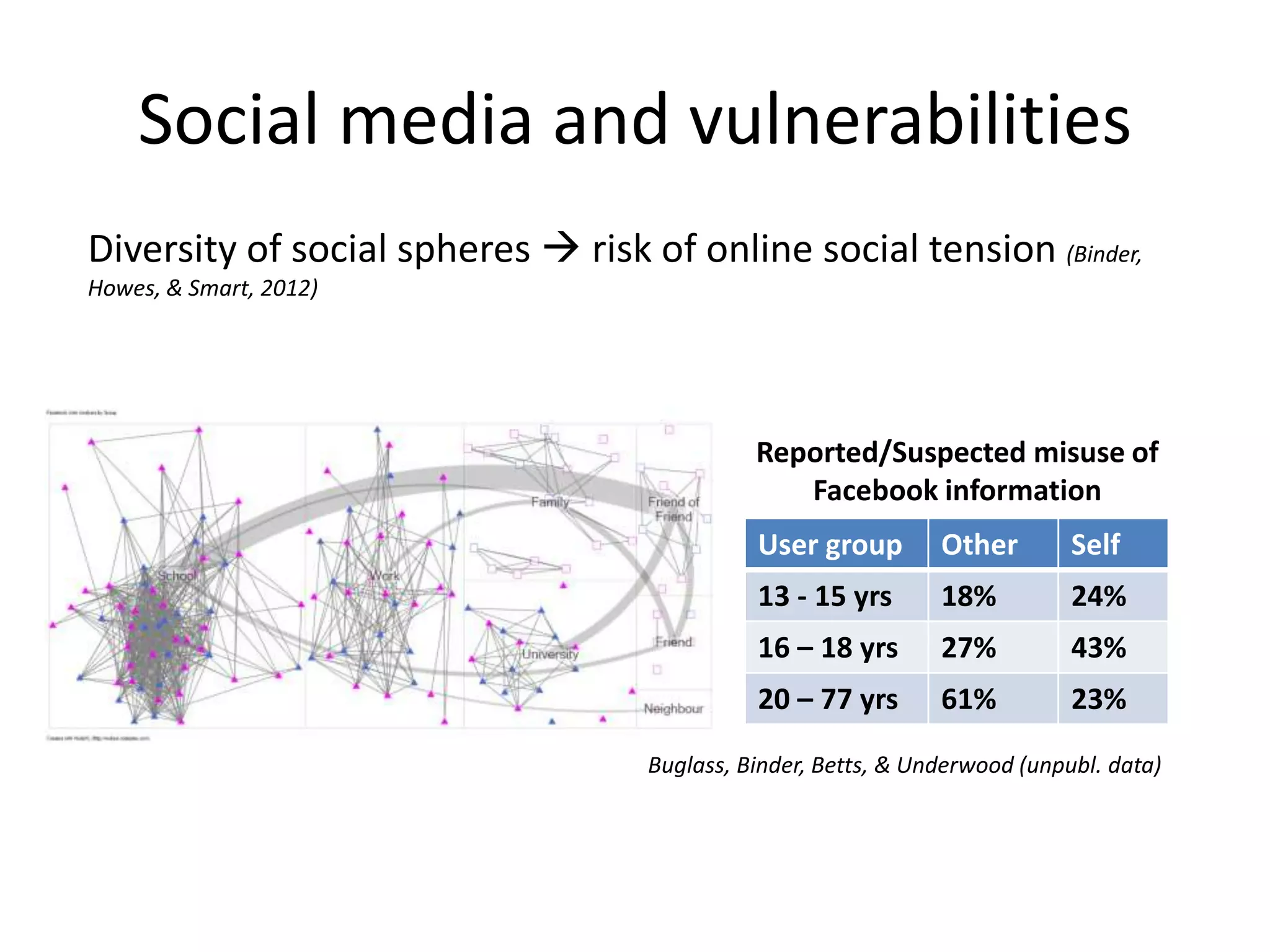
- Online Harassment and Abuse: This can include cyberbullying, online harassment, or hate speech, which can have severe consequences for mental health and well-being.
- Personal Data Breaches: These occur when sensitive information, such as social security numbers or financial information, is accessed without authorization.

Protecting Online User Behavior: Essential Tips
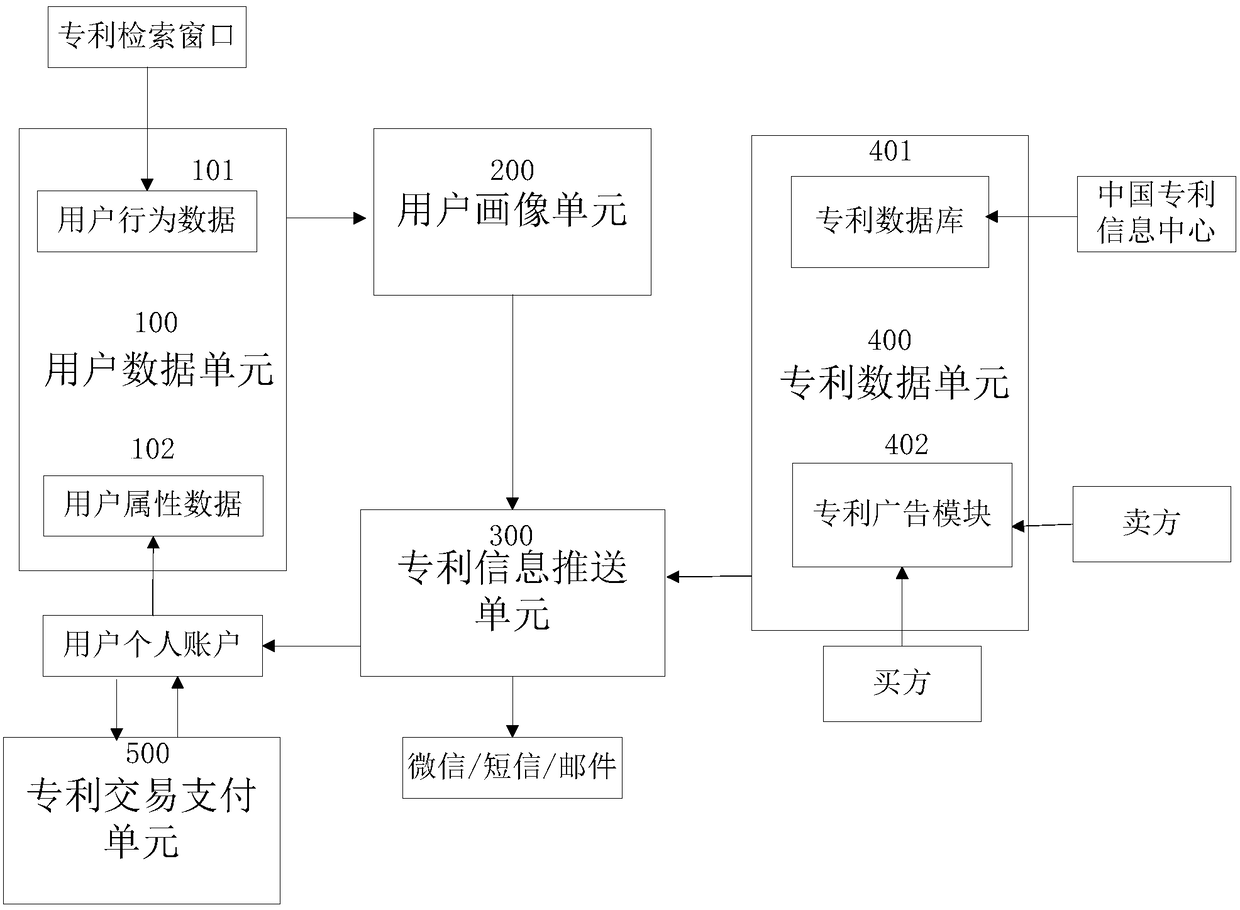
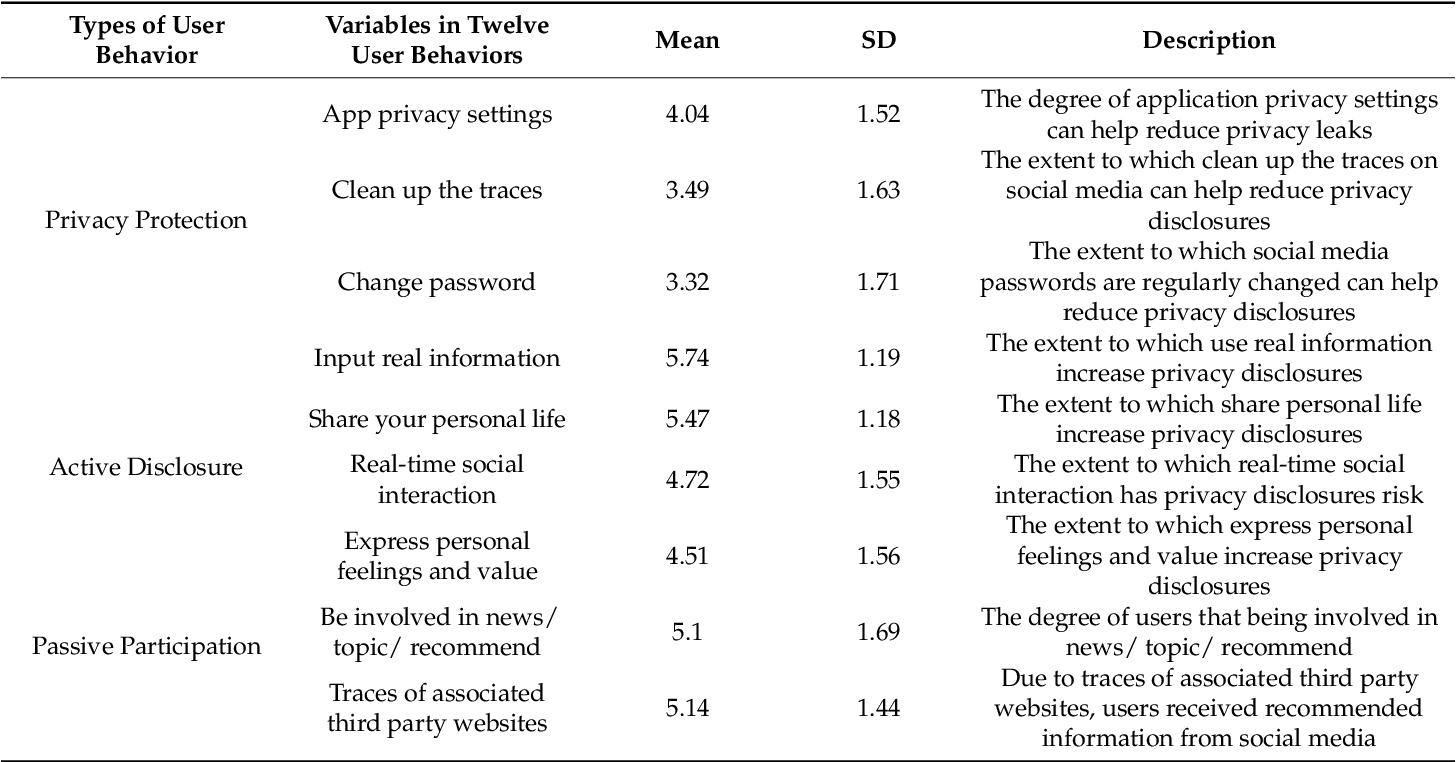
Furthermore, visual representations like the one above help us fully grasp the concept of Protect Online User Behavior.
Protecting online user behavior requires a proactive approach, which involves being aware of the potential risks and taking steps to mitigate them. Here are some essential tips to help you protect your online presence:Protecting Online User Behavior: Organization-wide Approach
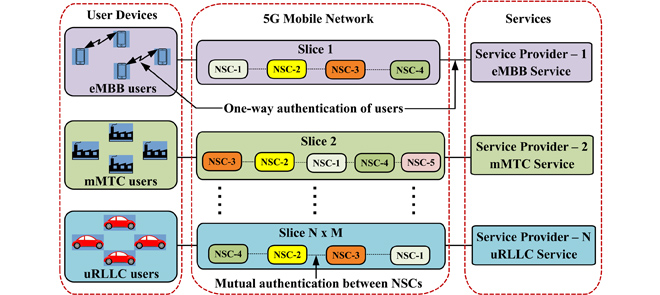
Protecting online user behavior is not just an individual responsibility but also a collective effort that requires the involvement of organizations and companies. Here are some steps organizations can take to protect online user behavior:- Implement Awareness and Training Programs: Educate employees on online safety best practices, such as identifying phishing emails and secure browsing habits.
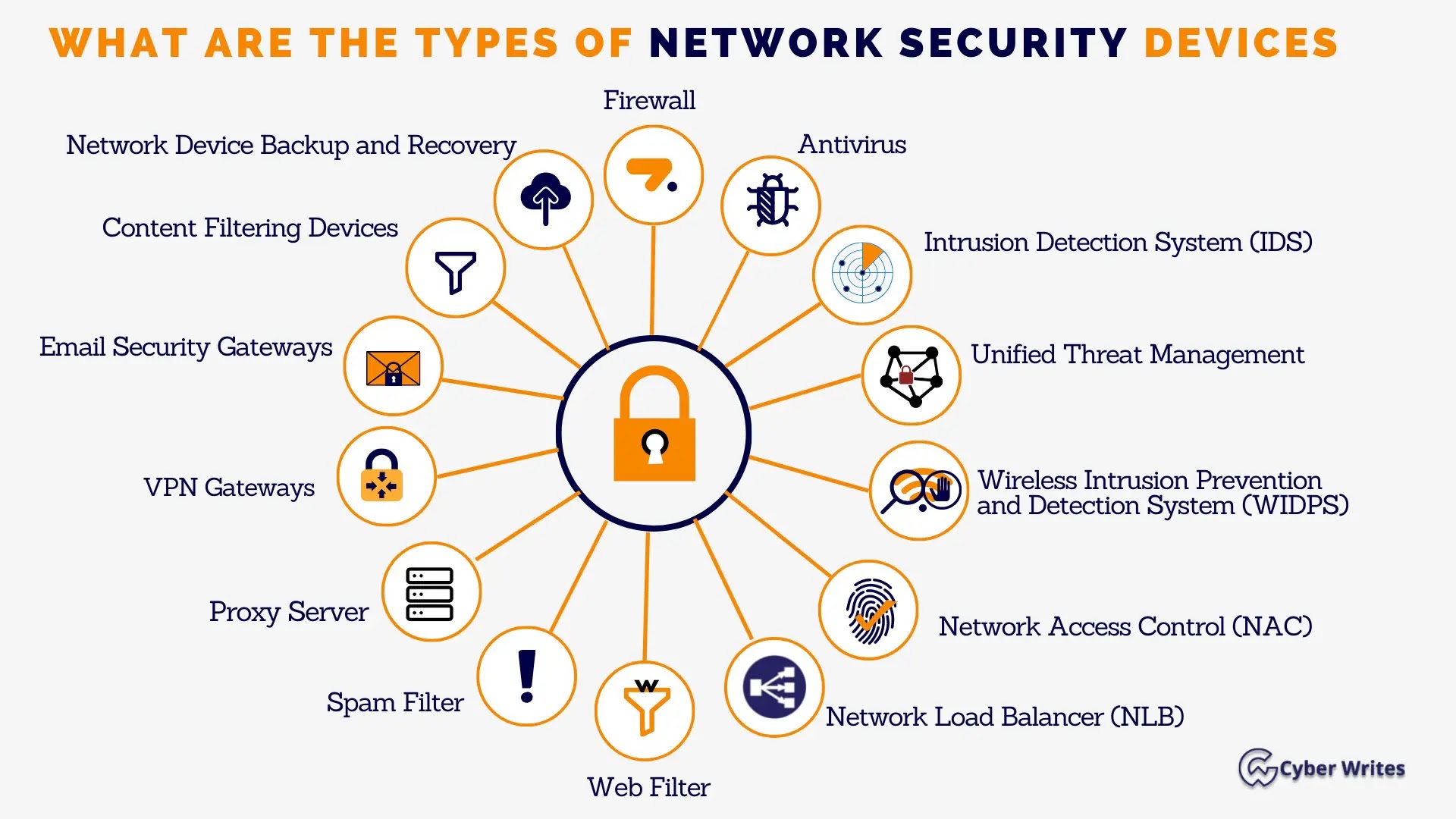
- Enable Security Measures: Install anti-virus software, firewalls, and intrusion detection systems to protect against malware and other online threats.
- Conduct Regular Security Audits: Regularly review and update security policies and procedures to ensure they are effective in protecting online user behavior.
- Develop Incident Response Plans: Establish protocols for responding to online threats and data breaches to minimize the impact on users and the organization.



)

![[PDF] A study of the User Privacy Protection Behavior in Online ... [PDF] A study of the User Privacy Protection Behavior in Online ... - Protect Online User Behavior](https://ai2-s2-public.s3.amazonaws.com/figures/2017-08-08/eb04c5e19e2ba1f5fcd1cc5a69360f76b879a651/6-Table2-1.png)